Table of Content
Now that you have the basics of iptables down, we recommend you check out our knowledge base for more commands that you can use with the program . Simply put, a firewall can stop unwanted connections to your site, if you know how to spot them. In today’s world, where sites are under constant attack, a firewall can be one of your best defenses against intrusions. Public assumes that the network is shared with the World and is the most restrictive profile.
The device is incredibly reliable, too; the slow performance won’t ever let you down. It’s referred to by the company as The Vault, as it’s a small form factor PC built for hardware firewall and router use. You get 32GB of storage and 4GB of RAM, although most customers upgrade the RAM to 8GB for faster speeds. You don’t need to do this, though; you will still get a fast and reliable firewall. Some of the advanced settings can be difficult to set up for first-time users. Kicking off our list today is the Ubiquiti Unifi Security Gateway firewall.
Ways to Implement a Server Firewall
A firewall throughput applies to hardware firewalls and usually offers a range of firewall throughputs to choose from. Entry-level to midrange hardware firewalls will have a throughput of roughly 500Mbps. For even more peace of mind, TP-Link’s router also comes with a lifetime warranty. You never need to worry when using it as you are protected should anything happen. There is also 24/7 technical support available, for free, so you are never in the dark or struggling. There’s a range of open-source software that you can install on this device, such as dd-wrt, FreeBSD, ClearOS, CentOS, OpenVPN, pfsense, and more, offering you fantastic customizing opportunities.
Power Packs are updates that add new features and provide fixes to known issues for Windows Home Server. When you open up WHS Console, you’re prompted to log into the server. There are a few other features here to like having the password remembered, password hint, and resetting the console.
Is It Worth Having A Firewall At Home?
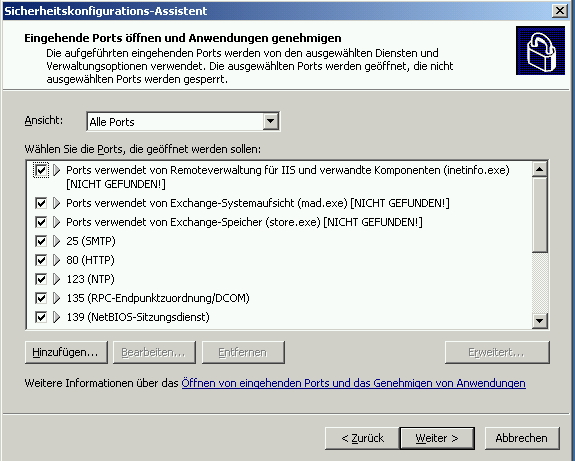
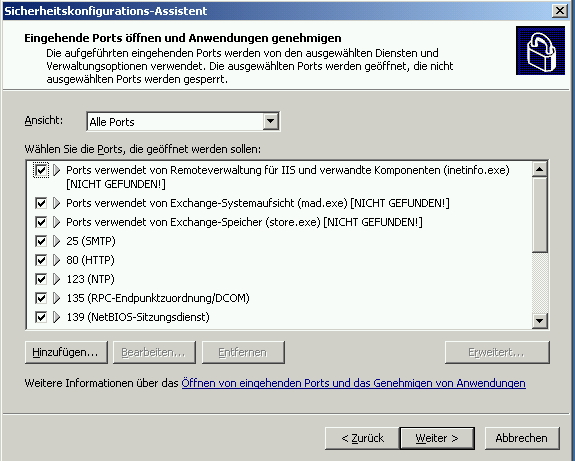
A number of additions were made to Group Policy, so that Windows system administrators could configure the Windows Firewall product on a company-wide level. XP's Windows Firewall cannot block outbound connections; it is only capable of blocking inbound ones. Once you know how to open or forward the ports you can use the application name, port numbers or port ranges, tcp/udp protocols shown here to modify your firewall or router's settings. To bookmark this page for future reference, press CTRL+D, alternatively you can make a note of the required tcp/udp ports now, unless stated otherwise, all the ports listed above must be forwarded.
This is always the case with the machine where you are creating the rule. Select ‘These IP addresses’ to state that the rule applies to the packets with an address specified in the list. You can later edit or remove any of the IP addresses in the list. Click Customize… and select to apply the rule to connections on all interfaces or chose one of the available interfaces listed in the box. This option blocks all network traffic that matches the firewall rule configuration. If a similar rule with ‘allow’ action is in place, then the block action has the priority unless otherwise is stated in the other rule.
Remote Coverage
Security log capabilities are included, which can record IP addresses and other data relating to connections originating from the home or office network or the Internet. It can record both dropped packets and successful connections. This can be used, for instance, to track every time a computer on the network connects to a website. This security log is not enabled by default; the administrator must enable it. In order to avoid firewall rule conflicts and configure a firewall correctly, you need to understand the sequence of existing firewall operation.
Unlike most Linux distributions, Windows does not come with the Python programming language by default. Goran combines his leadership skills and passion for research, writing, and technology as a Technical Writing Team Lead at phoenixNAP. Working with multiple departments and on various projects, he has developed an extraordinary understanding of cloud and virtualization technology trends and best practices. Click on New Rule… to start the New Inbound Rule Wizard.The wizard will let you choose the type of rule you want to create.
Remote coverage can also protect your devices when you are away from home and is definitely worth researching before purchasing your firewall. The router is integrated with Omada SDN software, allowing you to integrate network devices, gateways, access points, and switches. You can even choose your preferred method and customize it to suit your needs. After all, who wants a firewall that isn’t working in their best interest? There’s a range of modes that you can choose from, allowing you to have complete control.

You want to monitor and control traffic that is coming in and going out to maintain the highest level of security at all times. It’s a fantastic feature for those with multiple devices in their home or running a small business from their homes; now you are in charge and can see everything. While it’s an expensive choice for experienced users after a customizable and reliable router, the Protectli is the one for you.
Despite the small size, it is still a powerful firewall. The firewall comes with 4 Gigabit LAN ports and a Gigabit WAN port, making it the ideal choice for home or business. Like all firewalls, remote management and monitoring features are available through the Unifi Controller, also known as the Graphical User Interface . Alongside this, there are heaps of other features that allow you to create a safe space for your computer at home.
This represents the port on the local machine where you are creating this rule. The following step will allow you to specify the protocol and port for the traffic that this firewall rule will filter. Click Next after you select a protocol type and configure the settings.
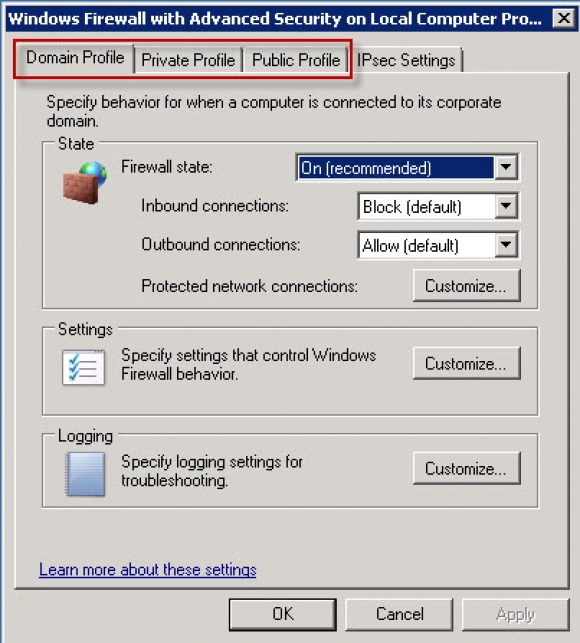
Windows Firewall with Advanced Security is the management console which stores all Windows Firewall configurations. Windows Firewall is a host-based firewall solution embedded with virtually all current Windows operating systems. For more information on how to configure your advanced policy firewall, take a look at our knowledge base, which includes more examples and guidelines. If you’re not a big fan of the command line, the Advanced Policy Firewall is an alternative that enables you to configure a firewall using a simple text editor. However, you’ll also need to use a particular program, and this one isn’t included by default on most Linux distributions . Keep in mind that while we support both of these types of firewalls at A2 Hosting, you’ll need root access to implement them.
The cool thing is that you can repurpose an older desktop to run Windows Home Server. A machine with a 1GHz Pentium III, 512MB of RAM, and an 80GB Hard Drive will work as the minimum requirements, but as you know minimum and recommended requirements are completely different things. You can check out the minimum and recommended system requirements from Microsoft’s WHS PDF guide . It’s best to consider how many network users there will be before purchasing your hardware to avoid any disappointment down the line.
This article explains the basic functions and different types of firewall and details the steps for managing the Windows Server Firewall within the Windows Firewall with Advanced Security interface. The Windows Firewall Management Console is a powerful tool that allows for creating detailed configurations. If you carefully followed the instructions in the article, you are now able to manage the firewall on your Windows Server. This field populates automatically after you select a protocol type, and you cannot change it. In order to insert your own port, select Custom in the ‘Protocol type’ dropdown menu. It is used when a computer connects to the corporate network.
IP tables enable you to grant or deny access to specific services and IP addresses. This provides you with full control over everything that goes in and out of your server, including Transmission Control Protocol and Secure Shell connections. In short, it’s going to be suitable for those who like to use the command line. The gateway device sits between the internet and local WiFi router, and its job is to route all traffic before it reaches the router. Here it can eliminate any prohibited or potentially threatening users, sites, or viruses, to ensure you remain safe. All devices connected to the device are protected and monitored thanks to advanced management and security features.

No comments:
Post a Comment